Compliance monitoring is widely misunderstood as a checklist exercise, a periodic scan through transaction logs that confirms what regulators want to see before moving on. In practice, it is far more demanding and consequential than that. Regulatory bodies expect financial institutions to build dynamic, institution-specific monitoring frameworks that evolve with their unique risk profiles, customer behaviors, and product portfolios. This article cuts through that misconception by offering risk and compliance professionals a clear, practical framework covering core concepts, effective tools, calibration strategies, and step-by-step implementation guidance designed for the real operational pressures you face every day.
Table of Contents
- Understanding compliance monitoring: Core concepts and regulatory context
- Key processes and tools for effective compliance monitoring
- Tailoring compliance monitoring: Calibration versus default settings
- Applying compliance monitoring: Practical steps for operational efficiency
- The practical realities most compliance teams overlook
- Unlock smarter compliance monitoring with AI-driven solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Tailored monitoring matters | Generic compliance settings miss unique risks; calibration is essential for regulatory success. |
| Tech pitfalls require vigilance | Fuzzy matching and AI misinterpretation can lead to compliance failures without oversight. |
| Annual rule tuning is expected | Financial regulators expect institutions to adjust transaction monitoring rules yearly using historical data. |
| Human judgment is vital | Despite advanced tools, human expertise is necessary to avoid operational blind spots. |
Understanding compliance monitoring: Core concepts and regulatory context
With that misconception cleared, let's start by building a clear foundation of what compliance monitoring truly means in today's financial landscape.
Compliance monitoring, at its core, is the structured, ongoing process of identifying, measuring, and managing an institution's adherence to applicable laws, regulations, and internal policies. For financial institutions specifically, it is not a static audit conducted once a year. It is a living function that touches transaction oversight, customer risk profiling, personnel behavior, third-party relationships, and regulatory reporting cycles, all operating simultaneously.
The regulatory context that frames compliance monitoring for most credit unions, community banks, and lenders centers heavily on the Bank Secrecy Act (BSA) and anti-money laundering (AML) obligations. BSA/AML requirements demand that institutions file Suspicious Activity Reports (SARs) when they detect potential illicit activity, and Currency Transaction Reports (CTRs) for cash transactions exceeding $10,000. Beyond those filings, risk-based customer monitoring requires institutions to assign risk scores to customers based on transaction patterns, geography, business type, and account behavior. As the OCC Bulletin 2025-37a confirms, regulators expect institution-specific calibration rather than reliance on default vendor rules, and that annual tuning of transaction rules using historical data is a baseline expectation, not a best practice bonus.
This matters because protecting trust with compliance is not just an ethical obligation; it is a core operational defense. A breakdown in compliance monitoring damages customer relationships, invites regulatory enforcement actions, and can destabilize an institution's market position quickly.
Key dimensions of a sound compliance monitoring framework include:
- Risk-based customer monitoring: Segmenting customers by risk tier and applying proportionate scrutiny based on transaction patterns and profile changes.
- Transaction surveillance: Continuously analyzing transaction data to detect anomalies against expected behavior or peer benchmarks.
- Annual rules tuning: Reviewing and adjusting monitoring thresholds using prior-period historical data, ensuring rules remain relevant as products and customer behaviors evolve.
- Regulatory reporting workflows: Maintaining accurate, timely SAR and CTR filing processes that are audit-ready at any moment.
"Compliance monitoring is not a control you install once. It is a discipline you maintain continuously, and regulators evaluate not just what your system catches, but how deliberately you have calibrated it to your institution's own risk reality."
For context beyond the domestic regulatory environment, the compliance significance for SMEs discussion in international markets reflects how universal these pressures are: regulatory complexity grows faster than most institutions can organically adapt, making structured monitoring frameworks an operational necessity rather than a regulatory luxury. Similarly, understanding how CECL compliance monitoring intersects with broader risk frameworks gives compliance teams a clearer picture of where monitoring obligations are expanding, particularly around credit loss estimation.
Key processes and tools for effective compliance monitoring
Understanding the foundation, let's explore the processes, tools, and nuances that drive effective compliance monitoring.
Effective compliance monitoring does not happen through a single platform or a single team. It requires interconnected processes, specialized tools, and robust governance structures working in coordination. The core workflow begins with data collection across all transaction systems, account management platforms, and customer interaction records, then flows into rules-based or model-driven analysis, alert generation, case management, investigation, and regulatory reporting.
The primary tools financial institutions rely on include:
- Transaction monitoring systems (TMS): Rule-based engines or machine learning models that flag transactions meeting defined risk criteria, such as structuring patterns, unusual cross-border transfers, or rapid fund cycling.
- Sanctions screening platforms: Tools that check customer names, entities, and transaction counterparties against government watchlists such as OFAC's SDN list, applying fuzzy matching logic to catch name variations.
- Customer risk scoring models: Automated engines that calculate and update customer risk ratings based on profile attributes, behavioral signals, and peer comparisons.
- Case management systems: Platforms where compliance analysts investigate alerts, document findings, and manage SAR filing decisions with full audit trails.
- Regulatory reporting automation: Workflows that compile and submit CTR and SAR filings to FinCEN with minimal manual intervention, reducing error risk and processing time.
Each of these tools carries inherent operational risks that compliance teams must actively manage. As RegTech case studies document, common edge cases include name variations in sanctions screening that require fuzzy matching logic to function accurately, large language model (LLM) hallucinations in AI-assisted compliance tools that can lead to misinterpretation of regulatory text, measurement bias in AML systems where postcode-based thresholds correlate with demographic data and create indirect discrimination risks, and governance failures in the software development lifecycle (SDLC) that introduce operational incidents when monitoring rules are updated without adequate testing protocols.
| Risk area | Common issue | Mitigation approach |
|---|---|---|
| Sanctions screening | Name variation misses | Fuzzy matching with confidence thresholds |
| AI-assisted tools | LLM hallucinations | Human review for regulatory interpretation |
| AML thresholds | Demographic bias | Geography-neutral threshold design |
| SDLC governance | Untested rule changes | Staged deployment with rollback protocols |
Pro Tip: Before deploying any AI-assisted compliance tool, define a human escalation protocol for all regulatory interpretation outputs. Models can surface patterns efficiently, but a compliance officer must own the final interpretive judgment.
Reviewing your compliance tools guide is a strong starting point for evaluating which platforms align with your institution's size, product mix, and risk appetite. Equally important is ensuring your security policy in compliance frameworks accounts for data access controls across all monitoring systems, since unauthorized access to sensitive transaction data creates both regulatory and reputational exposure.
Tailoring compliance monitoring: Calibration versus default settings
Now that we've examined operational tools and pitfalls, let's address the crucial topic of calibration and why customization matters for compliance monitoring.
One of the most consequential errors a financial institution can make is relying on out-of-the-box vendor monitoring rules without meaningful customization. Vendor defaults are designed to meet a broad market standard, covering enough ground to be defensible during an initial deployment. But they are not designed for your specific customer base, your transaction volume patterns, your geographic concentration, or your product risk profile. That gap between generic defaults and institution-specific reality is where regulatory exposure lives.
The risks of uncalibrated, default-vendor monitoring systems are significant and well-documented:
- Excessive false positives: Generic thresholds generate alert volumes that overwhelm compliance teams, causing genuine risk signals to be buried under routine noise, increasing the probability that a real SAR-worthy transaction is missed.
- False negatives that evade detection: Conversely, thresholds calibrated for a large bank's transaction scale may be entirely insensitive to the risk patterns typical of a community bank or credit union's membership, leaving material risks undetected.
- Regulatory criticism during examinations: Examiners who find institutions relying on unmodified vendor rules, without documented evidence of calibration rationale, will question the institution's risk management rigor and may issue matters requiring attention (MRAs) or formal enforcement actions.
- Misaligned customer risk ratings: Default risk scoring models often lack the granularity to reflect the specific risk indicators relevant to your institution's membership demographics, product usage, and service area.
The OCC Bulletin 2025-37a is explicit on this point: regulators expect calibration that is specific to the institution's own risk profile, supported by documented analysis of historical transaction data and validated against actual alert outcomes.
The calibration process, done well, involves a structured annual review of monitoring rule performance. Compliance teams should analyze the prior year's alert disposition data, specifically what percentage of alerts resulted in SARs filed, what percentage were closed as false positives, and what transaction patterns generated the highest risk-confirmed outcomes. That data directly informs threshold adjustments for the coming period.

| Monitoring approach | Alert accuracy | Regulatory defensibility | Operational efficiency |
|---|---|---|---|
| Default vendor settings | Low to moderate | Weak without documentation | Poor due to high false positives |
| Institution-specific calibration | High | Strong with documented rationale | Strong with focused analyst workloads |
Your custom calibration for compliance approach should be documented in a formal model risk management (MRM) framework, ensuring that every rule change carries a clear rationale, a backtesting result, and an approval chain. This documentation is what examiners review, and it is what separates institutions that demonstrate control discipline from those that simply operate monitoring systems reactively.
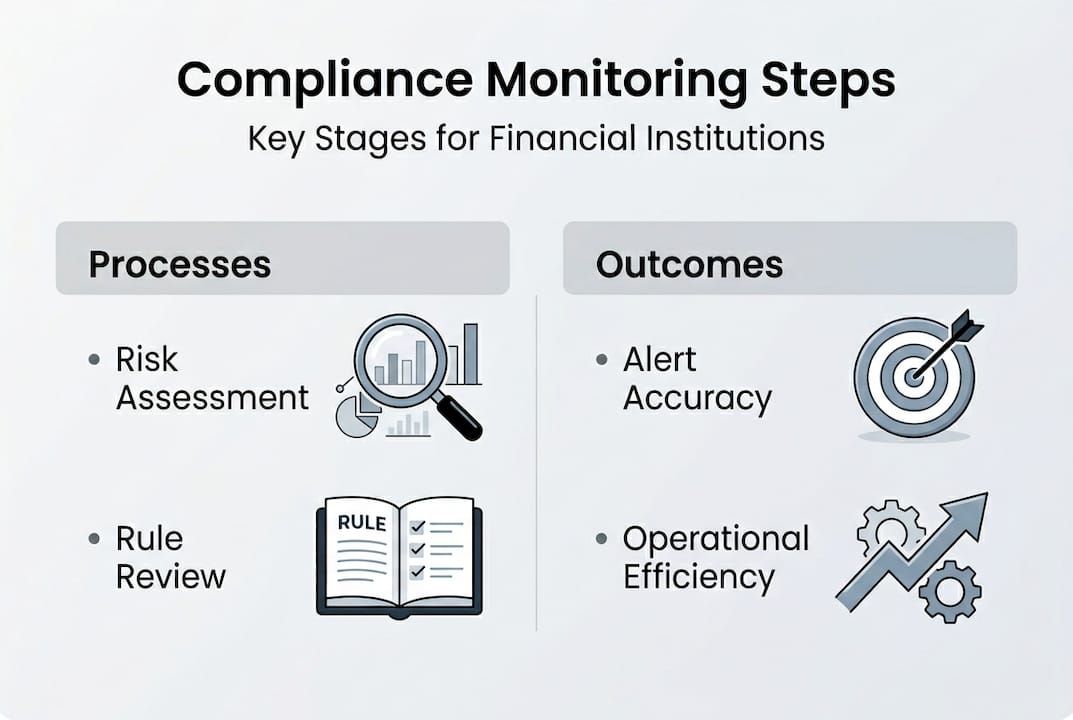
Applying compliance monitoring: Practical steps for operational efficiency
With calibration established as a necessity, let's focus on real-world steps for applying compliance monitoring and achieving greater efficiency.
Translating compliance monitoring principles into daily operations requires a structured implementation approach that balances regulatory rigor with the practical constraints of compliance team capacity and technology resources. The following sequence provides a foundation that risk and compliance professionals at community banks, credit unions, and lenders can adapt to their own operational context.
- Conduct a risk assessment baseline: Before configuring any monitoring tool, map your institution's inherent risk profile across products, geographies, customer segments, and delivery channels. This baseline determines where monitoring intensity should be highest and where lighter-touch controls may suffice.
- Define monitoring scope and rule logic: Based on your risk assessment, specify which transaction types, customer behaviors, and account patterns will trigger alerts. Align rule logic explicitly to BSA/AML regulatory expectations and internal policy thresholds.
- Configure and test in a staging environment: Never deploy new or modified rules directly into production. Test configurations against historical data in a staging environment, validating alert generation rates and comparing outcomes against known-risk cases from prior periods.
- Establish alert management workflows: Define routing, escalation, and investigation timelines for generated alerts. Assign clear ownership, document investigation standards, and maintain case records that are audit-ready from day one.
- Perform annual tuning using historical data: As confirmed by OCC guidance on annual tuning, regulators expect institutions to revisit and adjust transaction rules annually using prior-period data, ensuring ongoing relevance and regulatory defensibility.
- Document and report: Maintain formal records of all calibration decisions, alert disposition outcomes, SAR and CTR filing metrics, and examination-ready compliance reports.
Pro Tip: Run a structured false positive rate analysis each quarter, not just annually. Quarterly reviews surface threshold drift faster, allowing minor corrections before they compound into material compliance gaps at year-end tuning.
Building risk analytics best practices into your monitoring review cycle creates a continuous feedback loop between operational data and rule performance, which is the difference between a monitoring program that ages gracefully and one that becomes obsolete by the time examiners arrive. Complementing this with risk assessment automation tools reduces the manual burden of periodic reviews significantly, freeing compliance analysts to focus on case quality rather than data wrangling.
For institutions managing reporting obligations alongside monitoring, referencing a structured compliance reporting guide helps formalize the reporting cycle in ways that reduce last-minute preparation pressure and improve accuracy across regulatory submissions.
Efficiency in compliance monitoring is not about doing less work. It is about directing work precisely where risk actually concentrates, supported by tools and review cadences that keep your program calibrated, documented, and defensible year-round.
The practical realities most compliance teams overlook
Drawing from industry experience, it is worth examining the challenges that rarely appear in regulatory guidance documents but consistently shape whether compliance monitoring programs succeed or fail in practice.
The most persistent blind spot we observe is the belief that a well-configured system is a permanent system. Monitoring programs that are calibrated carefully at implementation and then left untouched gradually drift out of alignment with actual risk, as customer behavior evolves, new products launch, and fraud typologies shift. Static monitoring is decaying monitoring, and the decay is invisible until an examiner or an incident makes it visible.
Measurement bias deserves far more attention than it typically receives. As RegTech research documents, postcode-based AML thresholds can correlate with demographic characteristics, creating indirect discrimination risks that compliance teams often do not detect because their review processes focus on alert accuracy rather than alert equity. This is an emerging regulatory focus area that institutions should incorporate into their calibration documentation.
AI tools, including the kind increasingly embedded in platforms supporting AI-powered compliance transformation, bring real efficiency gains, but they require disciplined human oversight to prevent model confidence from substituting for genuine regulatory judgment. The most effective compliance programs treat technology as a force multiplier for experienced analysts, not a replacement for them.
Unlock smarter compliance monitoring with AI-driven solutions
If the processes and calibration strategies covered in this article reflect the complexity your compliance team manages daily, the right technology can transform that workload significantly.
RiskInMind's AI-powered risk management solutions are designed specifically for financial institutions navigating exactly these challenges. From automated regulatory automation workflows that reduce manual reporting burden to SOC 2 certified infrastructure that meets the security standards your institution demands, our platform is built to support compliance teams at credit unions, community banks, and lenders. Explore our SOC 2 compliance tools and see how RiskInMind can strengthen your monitoring program with accuracy, speed, and auditability at every step.
Frequently asked questions
What is compliance monitoring in financial institutions?
Compliance monitoring refers to the ongoing processes, tools, and reviews used to ensure financial institutions meet regulatory requirements such as BSA/AML, SAR, and CTR filings. As the OCC confirms, it includes risk-based customer monitoring and annual tuning of transaction rules using historical data.
Why is institution-specific calibration important in compliance monitoring?
Institution-specific calibration ensures monitoring systems adapt to the unique risk profile of each institution and satisfy regulatory expectations, avoiding the false positive overload and regulatory criticism that generic vendor defaults commonly produce. Regulators explicitly expect calibration beyond default vendor settings.
What are common pitfalls with compliance monitoring technologies?
Edge cases include name variation mismatches in sanctions screening requiring fuzzy matching, LLM hallucinations that misinterpret regulatory text, and measurement bias in AML systems where postcode-based thresholds create indirect discrimination, alongside governance failures that produce operational incidents.
How often should transaction rules be tuned for compliance monitoring?
Regulators expect annual tuning of transaction rules using historical data, ensuring thresholds and alert logic remain aligned with the institution's current risk profile and evolving customer behaviors.
